Today Manuel Fernandez is presenting HookME at Black Hat USA Arsenal 2013. HookME is software designed for intercepting communications which uses the Nektra Deviare Engine for binary instrumentation. HookME can intercept unencrypted HTTPS web traffic.
Many different proxy servers are used to intercept HTTP traffic. Fiddler is the most popular one for generic purposes. Burp Proxy is the leader for security testing. The issue with intercepting HTTPS traffic is that the proxy application acts as the man in the middle for HTTPS requests and the certificates being presented to the client are not the real ones. For example, intercepting network traffic to Amazon leads to a warning in the browser because the certificate being presented is unsigned. Another issue is that it is time consuming to set up the keys and certificates needed to configure the proxy.
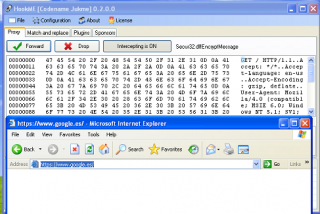
Instead of using a proxy developing a windows driver, you can intercept the EncryptMessage function in the Secure32.dll before it is encrypted as HookME does:
You can also intercept the WinINet.dll before data is encrypted in the HTTPS request, and after data is decrypted in the HTTPS response. This way, no change is made to any certificate and no man in the middle attack is simulated. These concepts are a starting point for more sophisticated web security, debugging tools, and support for Firefox and Chrome browsers. You can start by intercepting synchronous functions in WinINet.DLL such as InternetOpen, HttpOpenRequest, HttpSendRequest, HttpAddRequestHeaders, InternetReadFile, InternetWriteFile, and their “Ex” functions counterpart.
We also used this technique to monitor network traffic developing Data Loss Prevention Solutions.
If you liked this article, you might also like:
- SQL Server Interception and SQL Injection Attack Prevention
- Instrumenting Direct3D Applications to Capture Video and Calculate FPS
- Improving Deviare Hooking Performance with Custom Hooks
Related Nektra Products
Credits
These article and code would not have been possible without the support of our Windows driver development team and custom development software engineers.